Information security risk management and plan
Financial Information
Information security risk management and plan
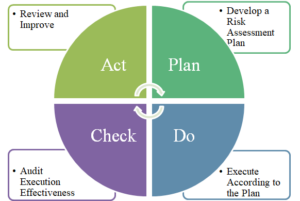
1.Information Security Risk Management Framework: The company’s information security unit is an independent department led by the General Manager as the highest organizational authority. This unit is responsible for coordinating and implementing information security policies, disseminating information security messages, and enhancing employees’ security awareness. The internal audit unit performs annual checks on internal control systems related to information cycles. The organizational operation model follows the PDCA (Plan-Do-Check-Act) cycle management approach to ensure reliability and continuous improvement.
2.Information Security Policy:To implement internal information security management, the company has established information cycle and information security management procedures with the following policy objectives:
(1) Protect the confidentiality, integrity, and availability of the company’s information assets.
(2) Regulate data access according to departmental functions to prevent unauthorized modification or use of data and systems.
(3) Ensure continuous operation of information systems, maintaining a certain level of system availability for critical core systems.
(4) Follow the PDCA model to ensure the implementation of information security.
3. Specific Management Measures:
(1) Internet Security Controls:
A. Deploy firewalls.
B. Regularly perform virus scans on computer systems and data
storage media.
C. Use network services according to information security policies.
D. Regularly review logs of network services and track any anomalies.
E. Continuously update virus definitions and operating systems.
F. Establish an Intrusion Prevention System (IPS).
(2) Data Access Controls:
A. Computer equipment should be managed by designated personnel
and require account and password settings.
B. Assign different access rights based on job functions.
C. Manage account creation and deletion in real-time.
D. Remove or overwrite confidential, sensitive data, and copyrighted
software before decommissioning equipment.
E. Remote login to management information systems should be
approved and authorized.
(3) Disaster Recovery Mechanism:
A. Regularly review emergency response plans.
B. Conduct annual system recovery drills.
C. Establish system backup mechanisms, ensuring off-site backups.
D. Periodically review computer network security controls.
(4) Awareness and Training:
Regularly promote information security information to enhance
employees’ security awareness.
4. Resources Invested in Information Security Management:
(1) Computer servers and application servers are housed in a dedicated
data center, with access logs maintained.
(2) Important equipment, such as firewalls, mail servers, and internal and
external network systems, are deployed with high-availability
architectures to avoid single points of failure.
(3) Deploy control accounts for information systems login and resource
access.
(4) Install antivirus software on servers and client devices, and update
virus definitions in real-time to prevent threats.
(5) Deploy firewalls, IPS, and spam filters to block spam and malicious
network activity.
(6) Conduct information security training to promote employee awareness
and reinforce their understanding of related responsibilities.
(7) Information personnel participate in regular disaster recovery drills.
(8) Hire professionals for vulnerability scans and penetration testing to
ensure server security.
(9) Use uninterruptible power supplies (UPS) and off-site data backup to
ensure continuous operation of critical resources.
(10) Implement data encryption mechanisms for the company’s website to
ensure secure data transmission.
(11) Join the Taiwan Computer Emergency Response Team (TWCERT).
(12)The company implemented ISO 27001:2022 in 2024 and obtained third-party certification.